Helo mate, long time no see. For this post i wanna write article that different with my other article. With my new jobs as Security Analyst in one of Security Company at Jakarta. In this topic i will talking about SIEM,
What is SIEM?
“is a term for software products and services combining security information management (SIM) and security event management (SEM). SIEM technology provides real-time analysis of security alerts generated by network hardware and applications. SIEM is sold as software, appliances or managed services, and are also used to log security data and generate reports for compliance purposes.” ~Wikipedia~
I heard from my friend, he is senior analyst in my company, SIEM is maybe something like point central for logging packet from IDS (Intrusion Detection System) and IPS (Intrusion Prevention Systems). So SIEM will collect all packet that came from IDS, IPS and other device that can integrated to this apps and report and generate reports for compliance purposes.
In further explanation SIEM is not just apps for collect logs packet. With SIEM we can do all of things related of security services like real-time monitoring, correlation of event, notifications, analysis and reporting of log data and many things capabilities that we can use from SIEM, commonly know as Security event management (SEM) and security information management (SIM). Of course that service is limited from SIEM product that used.
SIEM got input data from other device in the network, by example IDS, Firewall, Switch and the other devices.
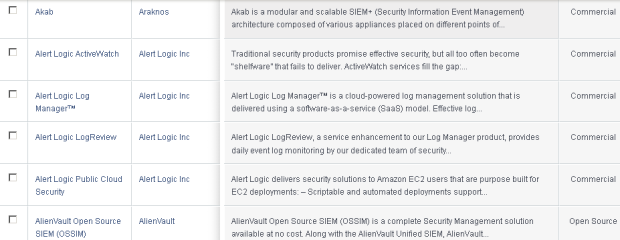
Oh ya, i forgot to tell you something. SIEM product is not just as application, some SIEM product is Appliance (hardware). SIEM feature is limited from that SIEM product and licence used. Here is example of SIEM product, you can see all of SIEM in here http://mosaicsecurity.com/categories/85-log-management-security-information-and-event-management
 Here is feature by usuallly brings on SIEM products :
Here is feature by usuallly brings on SIEM products :
- Data aggregation : Log management aggregates data from many sources, including network, security, servers, databases, applications, providing the ability to consolidate monitored data to help avoid missing crucial events.
- Correlation : looks for common attributes, and links events together into meaningful bundles. This technology provides the ability to perform a variety of correlation techniques to integrate different sources, in order to turn data into useful information. Correlation is typically a function of the Security Event Management portion of a full SIEM solution
- Alerting: the automated analysis of correlated events and production of alerts, to notify recipients of immediate issues. Alerting can be to a dashboard, or sent via third party channels such as email.
- Dashboards: Tools can take event data and turn it into informational charts to assist in seeing patterns, or identifying activity that is not forming a standard pattern.
- Compliance: Applications can be employed to automate the gathering of compliance data, producing reports that adapt to existing security, governance and auditing processes.
- Retention: employing long-term storage of historical data to facilitate correlation of data over time, and to provide the retention necessary for compliance requirements. Long term log data retention is critical in forensic investigations as it is unlikely that discovery of a network breach will be at the time of the breach occurring.
- Forensic analysis: The ability to search across logs on different nodes and time periods based on specific criteria. This mitigates having to aggregate log information in your head or having to search through thousands and thousands of logs.

